Assembly Language Programming for Reverse Engineering
Last updated 7/2023
Duration: 12h30m | .MP4 1280x720, 30 fps(r) | AAC, 44100 Hz, 2ch | 8.78 GB
Genre: eLearning | Language: English [/center]
Understand assembly code and modify exe files to add new functionality using x64dbg
What you'll learn
Assembly Language Basics
Reverse Engineering
xdbg debugging basics
Modifying programs
Injecting code into exe files
Hollowing out an exe file
CPU registers
Basic Addition
INC, DEC, MUL and DIV instructions
Accessing main memory (RAM)
The Stack
Function Calls
Input and Output Functions
Code Caves
Functions that returns a value
The Flags Register
Jumps
Compare Instructions
Structured Programming
Signed Operations
and more . . .
Requirements
PC
Basic C programming knowledge would be helpful but not necessary
You will learn everything you need to know
Description
If you have been using debuggers to reverse engineer programs but wished you had more understanding of Assembly Language, then this course is for you. We will cover enough assembly language to allow you to understand how to
modify
exe files to insert your own code or, to modify existing exe files to do things which it was not intended to do.
Traditionally, assembly language programming is taught using an assemblers like NASM or FASM. But learning it that way will not give you the skills to understand reverse engineered programs. There is a missing link (knowledge gap) of how to apply your assembly knowledge to modify programs. This course fills that knowledge gap.
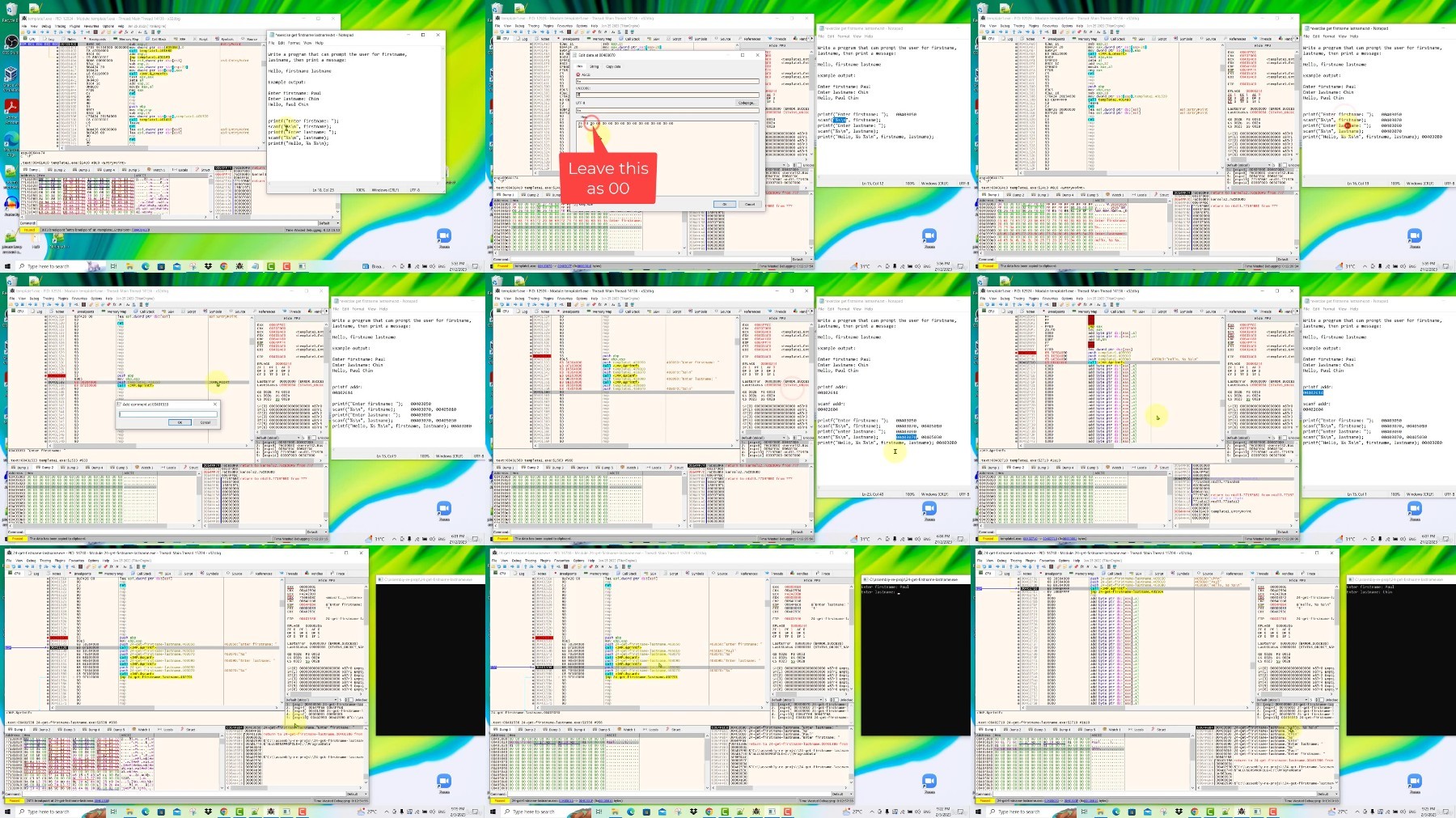
Instead of using an assembler, we will directly use the x64dbg debugger to learn assembly language. That is right, we will write our own assembly code inside the x64dbg debugger itself. You will learn Assembly Language from the ground up with zero knowledge as a complete beginner.
We will use techniques that allow you to:
modify existing code
overwrite existing code
modify memory segments to insert data
create new functions
exploit code caves
add new functionality to existing programs
and more.
This black art is not widely taught and there are no existing courses elsewhere that puts together coherently all the knowledge of assembly and reverse engineering. Mostly what you will find are separate courses on Assembly and Reverse Engineering. Many courses on Reverse Engineering don't cover the background assembly language from a software hacker's perspective. And almost all Assembly Language courses teach you how to write programs from scratch, instead of how to modify existing programs to add new functionality with your own code using a debugger like x64dbg.
The knowledge you gain will be your added advantage either as a security researcher, or, malware analyst, or student of software security. It will also benefit programmers who want to know how programs run internally and how to extend program functionality if you do not have the source code.
Go ahead and enroll now and I will see you inside!
Who this course is for:
Security researchers and students
Reverse Engineers
Anyone interested to learn Assembly Language from a software hacker's perspective
More Info
https://rapidgator.net/file/8438ba8...guage_Programming_for_Reverse_Engineering.z01
https://rapidgator.net/file/87af0aa...guage_Programming_for_Reverse_Engineering.z02
https://rapidgator.net/file/26c36df...guage_Programming_for_Reverse_Engineering.z03
https://rapidgator.net/file/278a3b5...guage_Programming_for_Reverse_Engineering.z04
https://rapidgator.net/file/bab88df...guage_Programming_for_Reverse_Engineering.zip
https://voltupload.com/1phpnn58n6je/Assembly_Language_Programming_for_Reverse_Engineering.z01
https://voltupload.com/n5kqxaux1uql/Assembly_Language_Programming_for_Reverse_Engineering.z02
https://voltupload.com/ajbpalocfj1u/Assembly_Language_Programming_for_Reverse_Engineering.z03
https://voltupload.com/qwkrgs5vb39k/Assembly_Language_Programming_for_Reverse_Engineering.z04
https://voltupload.com/330ykjm2rbcj/Assembly_Language_Programming_for_Reverse_Engineering.zip
Free search engine download: Assembly Language Programming for Reverse Engineering

